06
AugGrab Deal : Flat 30% off on live classes + 2 free self-paced courses! - SCHEDULE CALL
Penetration testers, or pen testers, carry out deceptive cyberattacks on an organization’s computer systems and networks. These legitimate penetration tests help to identify security vulnerabilities and weaknesses before any malicious attacker can get a chance to exploit them.
The role of a Penetration Tester is to identify the major gaps and weaknesses of a Test Case. If you are a penetration tester, you are the biggest asset of your testing team. $117,506 is the average entry-level salary of a penetration tester in the USA. The compensation is equally good in the areas of Australia, Canada, India, etc.
A career as a pen tester mostly starts with an entry-level cybersecurity position. In today’s blog, we’ll thoroughly discuss what penetration testing is and what precisely the penetration testers do, why this is considered an in-demand cybersecurity career, how to begin and how it could be a good fit for you, and how to get started and what skills you will require.
The testing job market has immense demand for Penetration testers. A few studies say that the demand for Penetration Testers have increased from 17% in the last year to 21 % this year. Hence, you must join Cybersecurity Training & Certification Course that will help you to build a strong foundation in the Cybersecurity domain.
Numerous parts of cybersecurity knowledge request human information. Cybersecurity is a human-driven issue and relies upon having HR that can see how the trouble makers think. In the realm of cybersecurity, the infiltration analyzer is now and then compared to a moral programmer because specific parts of the activity require replication of what a malignant programmer would do.
Entrance testing, as a control, is critical in the general security system of an association. It is utilized to spot issues and vulnerabilities in IT frameworks, including web applications. For the most part, computerized instruments are utilized to help with the procedure to discover security holes in an association's IT framework.
In any case, numerous pentesters (particularly experienced ones) will utilize manual techniques to expand and broaden the compass of computerized tests. Pentesting reproduces how a cybercriminal would utilize security imperfections to assault a foundation to get access to information and resources.
If you’re planning to make a career in CyberSecurity, but are not sure whether a career in Cyber Security is a good choice or not? Go through Cyber Security As A Career Option: Here’s the What You Should Be Knowing blog, where you’ll find every detail related to a cybersecurity career.
The job of entrance analyzer is one that requires incredible obligation. You will be depended upon to have wide learning of cybersecurity systems, danger types, and vectors. As the cybersecurity scene is one of the most liquid and constantly changing enterprises on the planet, you should be set up to be ceaselessly refreshing your insight into the region. This implies you should be extremely inspired by cybersecurity and arranged to learn constantly.
You additionally should have the option to comprehend IT frameworks and systems at a profound level. Understanding correspondence conventions is additionally significant, as this can be a feeble point in a framework.
It implies having the option to compose a helpful programming code. It may not be significant, and you should not be great at it; however, having working information from a scripting language like Python will be handy.
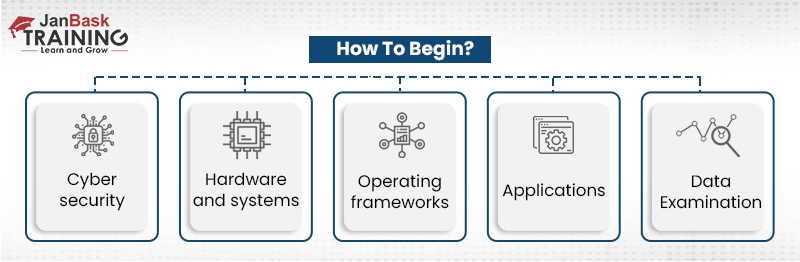
Regardless of whether you are a tenderfoot or a prepared IT expert contemplating moving into pentesting, you should start by finding out about the subject. Use articles, course readings, and aides, and discover recordings regarding the matter — on pen testing as well as on general cybersecurity issues in all cases.
There are likewise fantastic sites by cybersecurity security masters, for example, Bruce Schneier, and assets like the Hacking Articles blog.
Eventually, pen testing is a common-sense subject. Every one of the books on the planet and all the YouTube recordings on moral hacking won't set you up for the genuine article. You should get practice. On the off chance that you have come this far, there is a high possibility you will be one of those individuals who will have the option to effortlessly actualize your own smaller-than-normal test framework.
Use a pen testing toolbox, for example, Security Onion or Kali Linux, to begin playing out your pen-testing for training. They offer a typified set of pen testing devices that you can use to feel your way around the down-to-earth side of pen testing.
Additionally become acquainted with the Penetration Testing Execution Standard (PTES), which is a system for pen-testing. It can assist you with working towards guidelines of activity and is a decent broad warning in the field. Numerous employments will require you to be completely mindful of this standard just as OWASP.
When you are prepared, you can take a course to gain a moral hacking affirmation, for example, the Certified Ethical Hacker (CEH) confirmation. It will give any imminent business confirmation that you have the critical learning of the zone and the skill to apply it essentially.
It might also be helpful to take affirmation courses in systems administration and security.
Pentest+ accreditation is another alternative. It's optimal to give you the skill in doing infiltration testing.
To get certified, you need skills. You can easily learn those skills by taking an online course.
Browse through the website of JanBask Training and opt for their Cybersecurity course that covers penetration testing too.
Usual Roles and Responsibilities of a Penetration Tester
Entrance analyzers are normally present in the internal team of ab association and will sit inside a security group.
Entrance testing isn't just about discovering imperfections in systems and web applications. It is likewise about conveying your discoveries, both to colleagues and the executives in different offices.
There might be varieties in the job of pentester crosswise over industry parts, yet there are principal assignments that you will perform. These include:
Web Applications assume an imperative job in current associations today as increasingly more programming applications are conveyed to clients employing an internet browser. Essentially all that you may have done on the web includes the utilization of a web application - regardless of whether that was to enroll for an occasion, purchase things on the web, take care of your tabs, or even mess around.
Because of the wide usage of web applications, they are ordinarily the #1 most assaulted resource on the web and as a rule represent a wide scope of trade-offs, for example, Panera Bread and the Equifax Breach.
Is it genuine that these ruptures could have been averted? Truly! In any case, just if the web applications were altogether tried either inside or by a counseling firm. However and still, after all that - such vulnerabilities could have been missed.
A Network Pentest expects to recognize and abuse vulnerabilities incorporate or modern systems just as in system gadgets and the hosts/frameworks associated with them. Such appraisals, for the most part, mimic a certifiable assault if a programmer was to access the inner system of an organization.
Presently, can a system be 100% sheltered and secure? Obviously not! Nothing is 100% secure! For instance, we should take the Hacking Team Breach. Any modern assailant with sufficient opportunity, cash, and assets can break an organization; yet that doesn't mean it ought to be simple for them once they are inside the system!
Another model would be of the NotPetya Malware breakout in Ukraine. This is an incredible case of how programmers with sufficient opportunity and asset can bargain an organization and use them to further do more assaults against different targets.
As a pentester, you are tasked with surveying the danger of a genuine break, which isn't just about getting Domain Admin on the DC but about verifying what sort of complete information is unprotected and out in the open because information security is of prime importance.
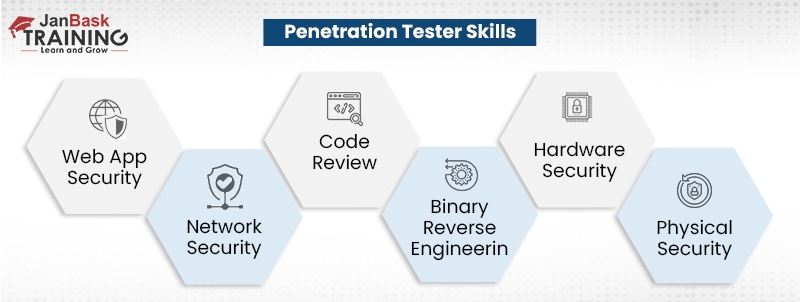
Code survey is presumably the absolute best system for distinguishing vulnerabilities and misconfigurations in applications. A manual audit of the code alongside the utilization of mechanized testing apparatuses can help find imperfections that may have never been found while doing a black box pentest -, for example, rationale defects, approval issues, encryption misconfigurations, and even infusion assaults.
The main drawback to Code Review is that it's very tedious and a solitary analyzer probably won't have sufficient opportunity to cover the entire application if it's exceptionally huge. To battle this, an analyzer, as a rule, attempts to concentrate on known vulnerabilities and the use of hazardous capacity brings in the language the application is written in. For instance, in C we realize that the strcpy() work is known to be defenseless against cradle floods, or in PHP, the executive() work if not appropriately used can prompt Remote Code Execution.
Ahh indeed, Reverse Engineering, the unexplained wonders where a programmer peruses some bizarre, antiquated language and for some mysterious explanation makes an adventure or sees how the application capacities. Alright, perhaps not so much mysterious, and not an old language as well!
Parallel Reverse Engineering is the way toward dismantling an application to perceive how it functions to either misuse it or to discover explicit vulnerabilities. This training is currently every now and again used by pentesters when searching for 0days, or during commitment in specific ventures, or notwithstanding when source code isn't given. Through figuring out, an analyzer can figure out how the application plays out specific activities, stores information, or even keeps in touch with memory using a disassembler, for example, IDA Pro, Binary Ninja, and even Radare2.
You may imagine that Reverse Engineering is generally utilized for Malware Analysis, for example, in the WannaCry Malware to completely see how the malware capacities, yet that is truly not the situation! Malware is simply one more program/application, so at last, regardless you're turning around an application… only a noxious one.
Following intently in the strides of Reverse Engineering is Hardware/Embedded Devices which supplements Reverse Engineering truly well. The line that up with learning in equipment and hardware just as some ARM Architecture and you got yourself another gig destroying gadgets from switches to lights to even vehicles.
With the expansion in the improvement of IoT gadgets, there is presently a raised intrigue and contention about the security for such implanted frameworks. We should take the Mirai Malware, for instance, with a huge amount of shaky gadgets open on the web, an organization is basically one gadget away from a break. Yah, only one gadget, for instance when a club got hacked through its web associated fish tank.
You can have the best security on the planet, the most solidified frameworks, and the best security group there is nevertheless the majority of that is brought to nothing if an assailant can basically help out your servers through the front entryway. This is the place Physical Security comes in!
Be that as it may, truly, truly take one moment to survey this issue. We care about such a great amount about the security of our PC frameworks, web applications, and systems that we neglect to see the helplessness in the human and physical angle. Anybody can simply walk directly into an organization that has inappropriate security controls and take information, plant malware, or even do dangerous activities.
As a pentester, in case you're doing a physical security appraisal, you'll have to comprehend a wide assortment of subjects, for example, brain science, reconnaissance, lock picking, lock side steps, RFID, camera frameworks and utilization of widespread keys. General evaluations will expect you to study a physical area, discover passage/leave focuses, detail set up security, for example, monitors, cameras, weight sensors, movement sensors, closely following guards, and the sky's the limit from there.
Along these lines, with professional education and a few authentications under your name, you, at last, have some involvement. Be that as it may, is it enough? How might you get more?
Above all else, any important course work and testaments are generally sufficient to get you a lesser situation in security, yet are certainly insufficient to get you enlisted as a security expert/pentester without having any earlier working knowledge - except if, that is you are talented, have a great deal to appear, and can kill the meeting.
A considerable lot of the individuals that I work with, and those filling in as pentesters have at any rate 5-10 years of working knowledge doing things, for example, advancement, framework organization, arrange to build, security tasks (SOC), occurrence reaction, and even malware investigation/figuring out.
So does that mean you need numerous times of understanding to be a pentester? Not in any manner! Yet, you do need to have some conventional working learning. I began my activity as a Security Consultant with just around 3 years of security experience added to my repertoire, and in fact 5 years of "learning background".
Taking an experience can be anything from doing CTF's, perusing books, understanding system foundation and endeavor innovations, to rehearsing in labs. And keeping in mind that such experience is extraordinary, the genuine inquiry is - would you be able to incorporate such information?
In this blog, we learned what penetration testing is and what precisely the penetration testers do, why this is considered an in-demand cybersecurity career, how to begin and how it could be a good fit for you, and what skills you will require.
From here on, your immediate step should be to go for Online Cybersecurity Courses, and JanBask Training could be of great help. It is an elaborate training session that considers all the details you might require. The training session will give you great practical exposure. You will get the opportunity to learn and grow with individuals coming from several different parts of the world.
Q1. Why should you learn CyberSecurity?
Cybersecurity is a trending sector where there are a lot of opportunities going forward. Also, it’s a field with never-ending demand. Here are the top reasons to learn Cybersecurity:
Q2. Why learn CyberSecurity courses?
It’s a great choice to learn CyberSecurity because LinkedIn has over 2,000 Cybersecurity job openings for beginners and experts. CyberSecurity Analysts earn about US$76,410 per annum in the US, according to Glassdoor, and globally, Cybersecurity will create over 3.5 million new job openings this year.
Q3. Is CyberSecurity a good career?
With the rise in the sophistication and volume of cyberattacks in companies, the need for Cybersecurity professionals is only growing. Especially in organizations that have to safeguard information related to financial records, health, national security, etc., Cybersecurity professionals are in great demand. Therefore, Cybersecurity is one of the best career choices in the IT field today.
Q4. I want to make a career in CyberSecurity. Where should I start?
If you want to pursue a career in Cybersecurity and Ethical Hacking, you must start by registering for one of the best online CyberSecurity courses and become proficient in it. JanBask Training’s Online CyberSecurity Courses are designed especially for those individuals who wish to upskill themselves and build a career in this popular domain.
Q5. How to choose the right CyberSecurity certification for my career path?
Use the following simple steps to choose the CyberSecurity program that best suits you:
Q6. Which are the top industries suitable for those who are seeking a career in the field of Cybersecurity?
Few of the best industries for aspirants planning to make a career in CyberSecurity are:
Q7. Which are the top companies hiring Cybersecurity professionals?
Top companies that are hiring Cybersecurity professionals are:
Q8. What are the skills required to learn CyberSecurity?
A few of the skills required to learn Cybersecurity are:
Q9. What are the most in-demand CyberSecurity certifications in 2022?
Some of the most in-demand Cybersecurity certifications in 2022 are:
Q10. What are the various job opportunities available after these best online CyberSecurity courses?
Here are some of the job opportunities available after you complete your cybersecurity training:
 Pinterest
Pinterest
 Email
Email
With fact-finding market research & solicitous words, Nandita helps our digital learners globally navigate their way to profound career possibilities in IT and Management.

Cyber Security

QA

Salesforce

Business Analyst

MS SQL Server

Data Science

DevOps

Hadoop

Python

Artificial Intelligence

Machine Learning

Tableau
Search Posts
Related Posts
What is Selenium? Getting Started with Automation Testing in Selenium
![]() 3.7k
3.7k
What Is The Difference Between Test Plan and Test Strategy?
![]() 710.6k
710.6k
Difference Between Software Validation and Verification
![]() 241.3k
241.3k
Various Career Oriented Testing Certification
![]() 189.3k
189.3k
Cloud Performance Testing - A Comprehensive Overview (2023)
![]() 2.9k
2.9k
Receive Latest Materials and Offers on QA Testing Course
Interviews