24
JulInternational Womens Day : Flat 30% off on live classes + 2 free self-paced courses - SCHEDULE CALL
In this modern era of digitization, no business can survive without the inclusion of cloud computing technology. Businesses of all sizes are seamlessly migrating towards cloud computing for a variety of reasons. These include- reduction in costs, managing risk and improving data security. This creates the need to hire AWS certified professionals in every organization who can efficiently deal with cloud computing technology. Getting an AWS Certification Course will enable you to get deeper insights into the cloud computing technology and also upgrade your resume.
AWS is the cloud platform that has become everyone’s favorite in no time. Many factors have contributed to AWS's journey to fame in the cloud computing domain . Some of these factors are- flexible pricing modules, easy to use services, great support services, a huge community to solve issues, and much more. Today we shall discuss AWS VPCs. For this, we have divided the blog into the following segments-
A virtual private cloud (VPC) is a virtual system committed to your AWS account. It is sensibly disengaged from other virtual systems in the AWS Cloud. You can dispatch your AWS assets, for example, Amazon EC2 occasions, into your VPC. You can indicate an IP address extend for the VPC, including subnets, partner security gatherings, and arrange route tables.
A subnet is a scope of IP addresses in your VPC. You can dispatch AWS assets into a predefined subnet. Utilize an open subnet for assets that must be associated with the web, and a private subnet for assets that won't be associated with the internet.
To ensure the AWS assets in each subnet, you can utilize numerous layers of security, including security gatherings and system access control records (ACL).
A VPC is a virtual system explicit to you inside AWS for you to hold all your AWS administrations. It is an intelligent server farm in AWS and will have entryways, course tables, arrange access control records (ACL), subnets and security groups.
The major things to note are:
Willing to learn these technologies and sharpen up your skillsets, enroll for the best Cloud Computing certification now!
The first arrival of Amazon EC2 upheld a solitary, level system that is imparted to different clients called the EC2-Classic stage. Prior AWS records still help this stage and can dispatch occurrences into either EC2-Classic or a VPC. Records made after 2013-12-04 support EC2-VPC as it were. By propelling your occasions into a VPC rather than EC2-Classic, you gain the capacity to:
In case that your record support the EC2-VPC stage just, it accompanies a default VPC that has a default subnet in every Availability Zone. A default VPC has the advantages of the propelled highlights given by EC2-VPC and is prepared for you to utilize. If you have a default VPC and don't determine a subnet when you dispatch an occurrence, the case is propelled into your default VPC. You can dispatch examples into your default VPC without having to know anything about Amazon VPC. Despite which stages your record underpins, you can make your own VPC, and design it as you need. This is known as a nondefault VPC. Subnets that you make in your nondefault VPC and extra subnets that you make in your default VPC are called nondefault subnets. The best AWS certifications validates one’s expertise on the AWS platform and serves as a key to success. Here’s a list of the Top 10 AWS certifications that are in-demand in 2022.
When you open up an administration inside an open cloud, it is adequately open to the world and can be in danger to assaults from the web. To secure your occurrences and secure them against assaults, all things considered, you lock them inside a VPC. The VPC confines what kind of traffic, IP addresses, and furthermore the clients that can get to your instances.
This counteracts undesirable visitors getting to your assets and verifies you from things like DDOS assaults. Not all administrations expect access to the web, so those can be bolted away securely inside a private system. You would then be able to uncover just certain machines to the web.
Clearly, if you needed to introduce programming or access the web from private examples that are closed off from the web, at that point, this is an issue. Nonetheless, there are a couple of answers for this issue I will cover next.
AWS gives an elite, and low-dormancy private worldwide system that conveys a safe distributed computing condition to help your systems administration needs. AWS Regions are associated with various Internet Service Providers (ISPs) just as to a private worldwide system spine, which gives improved system execution to cross-Region traffic sent by clients.
The accompanying contemplations apply:
Network packet loss can be brought about by various elements, including system stream impacts, lower level (Layer 2) blunders, and other system disappointments. We engineer and work our systems to limit bundle misfortune. We measure parcel misfortune rate (PLR) over the worldwide spine that associates the AWS R.
Subnets resemble breaking an enormous system into sub-systems. Keeping up a littler system is simple when contrasted with keeping up a large network.
Take the case of an association. There are various groups, for example, Finance, Support, Operations, Technology, HR, Sales, and Marketing. The information open to the Technology group can't be given to the Sales and Marketing group; the information for the HR group can't be given to the Operations group and the other way around. Here, you make sub-systems with the end goal that, getting to and keeping up the system ends up being simpler.
AWS Architect certification course is the best to land you in one of the most lucrative jobs in the I.T sector. It will enable you to grab AWS entry-level jobs at the beginning of your AWS career path.
You can permit instances from your private subnet to interface with the web utilizing a NAT entryway. The examples in the private subnet don't have an IP address, so the NAT portal interprets the private IP to an open IP before directing the traffic out to the web. NAT represents Network Address Translation, and it does only that – interprets private IPs to open IP.
CIDR or Classless Inter-Domain Routing is utilized to designate IP address inside a system. We will utilize CIDR squares to check the scope of IP addresses for each subnet inside a VPC. The VPC itself would have a CIDR hinder that rundowns all the IP tends to accessible with it.
A routeing table contains a lot of guidelines, called routes, that are utilized to figure out where network traffic is coordinated.
Each subnet in your VPC must be related to a routeing table; the table controls the routing for the subnet. A subnet must be related with one route table at any given moment, yet you can relate numerous subnets with a similar route table.
Coming up next are the fundamental things that you have to think about route tables:
Check out for more blogs and resources at JanBask Training and see how AWS can be a game-changer for your career!
An Internet portal fills two needs: to give an objective in your VPC course tables for Internet-routable traffic and to perform network address translation (NAT) for occurrences that have been doled out open IPv4 addresses.
All together for the assets in a VPC to send and get traffic from the Internet, the accompanying conditions must be met:
Read our AWS tutorial to learn about the different skills and expertise needed for an AWS Architect
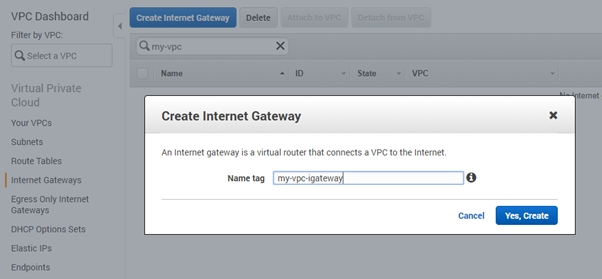
Pursue these means to join an Internet entryway to your VPC to empower correspondence of the open subnets with the Internet:
The first step is to go to the option of Navigate to the AWS console and then choose Services.
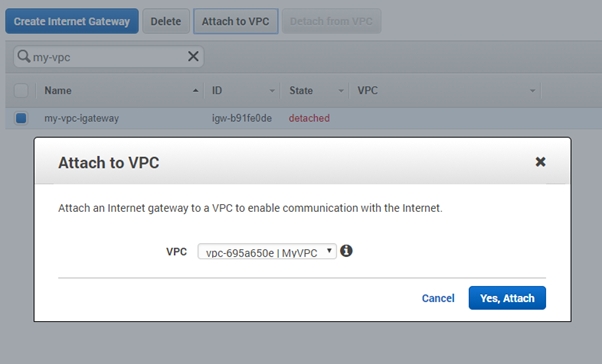
The internet gateway that you have just created is in a ;detached" state.
The next step is to attach it to your VPC securely.
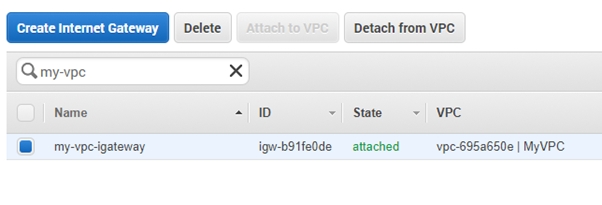
On completion, you will see that the status of the internet gateway now has been changed to "attached."
Learning AWS will definitely take your career to the next level. Getting the best AWS certification courses can become a life-changer for your career. But how long does it take to learn AWS? Check out from this blog!
How to Configure your own VPC(Virtual Private Cloud) in AWS?
At whatever point we log in to our AWS(Amazon Web Services) account a default VPC is made with the CIDR (172.31.0.0/16). VPC represents Virtual Private Cloud, it is virtual private system and is disengaged from other virtual systems in your AWS account, we can dispatch EC2, RDS and Elastic Cache occurrences utilizing our own made VPC.
Login to your AWS account, From the Services Tab, → Select VPC →then Select Your VPC → click on "Make VPC."
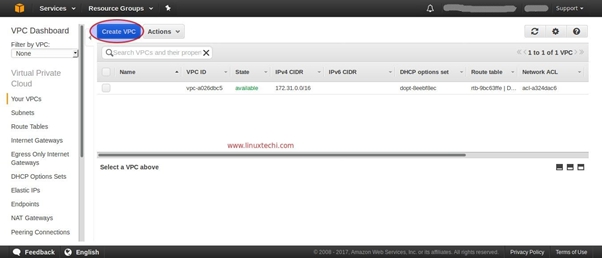
Indicate your VPC Name and CIDR (Classless Inter-Domain Routing), For my situation, I am utilizing the followings
192.168.0.0/24
Snap-on the option of “Yes, Create.”
In this progression, we will make two private subnets, Subnet1 (192.168.0.0/25) and Subnet2 (192.168.0.128/25) over the accessibility zones. We are calling these subnets as private since we can't access cases from the Internet at whatever point EC2 occurrence is getting IP from these subnets. Even though in the wake of appending Internet passage, these cases end up reachable over the internet.
From the VPC Dashboard click on Subnets choice and after that snap on Create Subnet
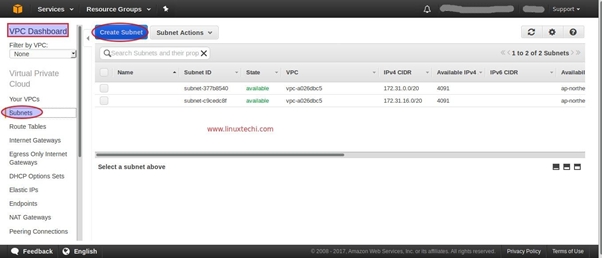
Once that is done specify the following after that
“192.168.0.0/25”
Choose the option of “Yes, Create”, in the same way, Create Subnet2 with IPV4 CIDR ;192.168.0.128/25”
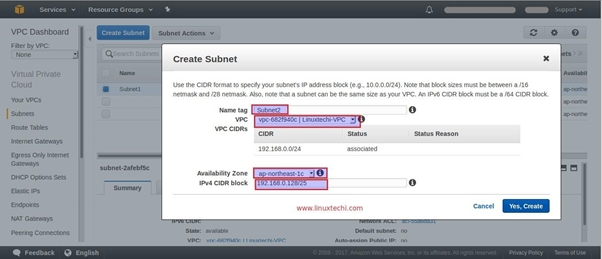
From VPC Dashboard there is an alternative to make a Route table. Snap-on "Make Route Table"
Determine the Name of Route Table and Select your VPC, For my situation VPC is Linuxtechi-VPC
Do you know that AWS is one of the most demanding careers in 2022? Getting a credible AWS certification will show your skills in cloud computing and help you to grab some of the well-esteemed job roles. But how much does an AWS Architect earn? Check here to know the details about an AWS Architect’s salary.
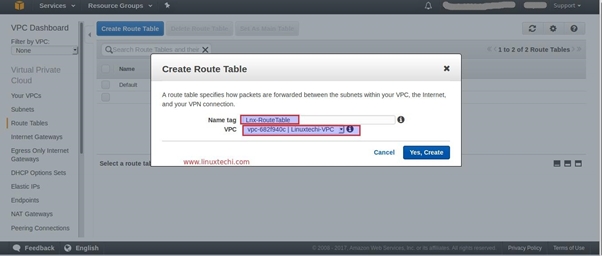
From VPC dashboard there is an alternative to make Internet entryway. Indicate the Name of an Internet gateway.

When the Internet passage is made, joined it to your VPC, Select and Right Click Your Internet entryway and after that, select the " Attach to VPC" alternative.
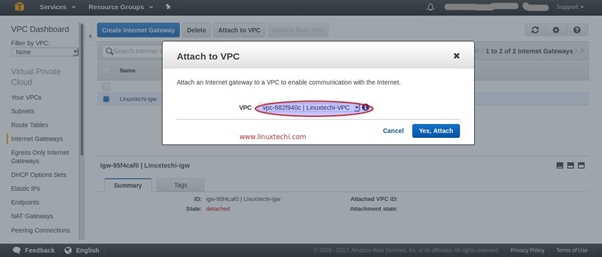
Presently Add Route to your course Table for Internet, go to Route Tables Option, Select your Route Table, For my situation it is "Lnx-RouteTable", click on Route Tab and Click on Edit and the snap-on “add another route.”
Notice Destination IP of the Internet as "0.0.0.0/0" and in the objective alternative, your Internet passage will be populated consequently as demonstrated as follows.
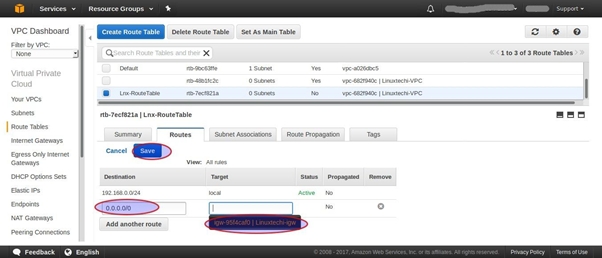
Click on Save option
Hey! It’s quiz time. Start with this free Quiz on AWS and check your subject knowledge. It’s fun and educational as well.
Step:5 Change Route table of your VPC Subnet
In the above advances we have made two Subnets (Subnet1 and Subnet2), I am going to change the course table of Subnet1. From the VPC Dashboard, Click on Subnets, Select the Subnet1 and the snap-on "Route Table" Tab and the snap-on Edit.
Change the default Route table to "Lnx-RouteTable" and after that Click On Save
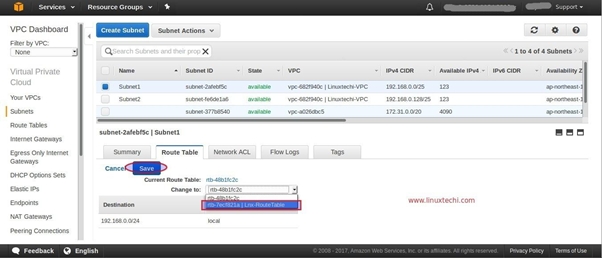
Presently onwards at whatever point an EC2 occurrence is propelled in your VPC utilizing Subnet1 then we can get to that case from Internet and Instance propelled utilizing subnet2 won't open over the Internet however it will be available inside.
Join our AWS community for more trending questions and latest updates.
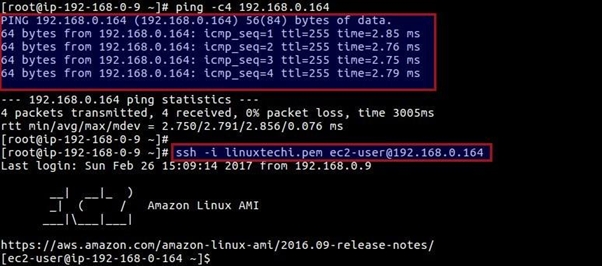
Dispatch APP Server in your VPC utilizing Subnet1 and DB Server utilizing Subnet2. Check whether you can get to APP Server and DB server from open IP.
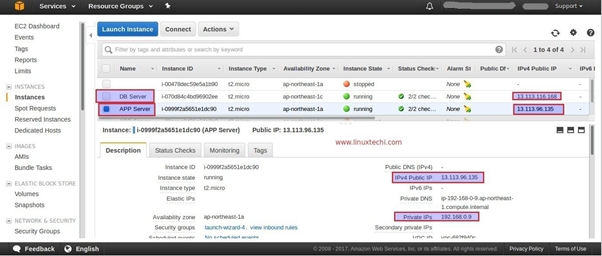
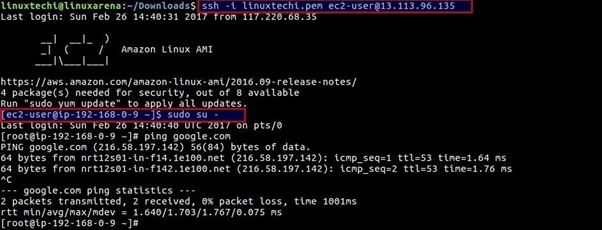
Try to SSH APP Server with its Public IP
Try SSH DB Server with its Public IP
linuxtechi@linuxarena:~/Downloads$ ping 13.113.116.168
PING 13.113.116.168 (13.113.116.168) 56(84) bytes of data.
^C
--- 13.113.116.168 ping statistics ---
Eight packets transmitted, 0 received, 100% packet loss, time 7056ms
linuxtechi@linuxarena:~/Downloads$ ssh -i linuxtechi.pem ec2-user@13.113.116.168
ssh: connect to host 13.113.116.168 port 22: Connection timed out
linuxtechi@linuxarena:~/Downloads$
We can't get to the DB server from the Internet since it is propelled with Subnet2 with its default Route table and Internet entryway isn't related to course table of Subnet2. Even though we can get to the DB Server from APP server with its private IP.
Are you preparing for your AWS interview? We have carefully crafted the Top AWS Solutions Architect interview questions and answers to upgrade your career as per the industry requirements.
Q1. What is AWS?
Ans- AWS or Amazon Web Services is a subsidiary of Amazon that specializes in cloud computing platforms that offer scalable and cost-effective cloud computing services. It provides distributed computing processing capacity and software tools to individuals and companies.This architect is the most flexible and secured cloud computing platform today.
Q2. What are the advantages of usingAWS?
Ans- Here are the advantages of using AWS-
i)Protects data
ii) Identifies management.
iii) Threat detection.
iv) Infrastructure protection.
v) Data compliance.
Q3. What are some of the features of AWS?
Ans- Some features of AWS are as follows-
i) Cost-effective.
ii) Scalability.
iii) Flexibility.
iv) Security.
Q4. What exceptional benefits will I get from an AWS training online?
Ans- Our online training of AWS is not just about introducing you with theoretical knowledge for qualifying a certification exam, our motive is to deliver you the knowledge that can be practically applied. We serve you with the knowledge that's around real-industry scenarios, case studies & practical assignments along with theoretical practice. We unfold you with real-time learnings that will make you ready for real-time use cases of the AWS techniques.
Q5. What is the necessity of AWS certifications?
Ans- AWS certifications are important to have as they:
Expand your job ready practical skills.
Gives boost while representing portfolio & CV to recruiters.
Maximize the possibility of getting hired over non-certified AWS Architects.
Help you demand your desired salary, as AWS certification reflects you have proven & competent skills.
Help you get great confidence while dealing with AWS solution architect jobs or real industry projects.
Q6. What skills will I be learning in this course?
Ans- Here are all that you will learn:
AWS Cloud Computing, AWS Architecture
Identity Access Management & S3
Amazon VPC, Elastic Compute Cloud (EC2)
Databases, Application Services, DynamoDB, Redshift
Configuration Management, Automation, AWS Route 53
Networking, Monitoring, Security Groups
Q7. What do AWS Developers do?
Ans- AWS Developers develop, migrate, and test AWS Cloud environments and integrate with other providers.They design and deploy solutions within AWS, while ensuring success during designing, building, and migrating applications, software, and services over the AWS platform and have robust use of services like EC2, EBS, Lambda, IAM, API Gateway, S3, DynamoDB, Elasticache, Step Functions, Kinesis, CFT, CloudFront, Load Balancers, AutoScaling, CloudWatch, CloudTrail, Elastic Search, VPC, etc.
Q8. What are the required skills for AWS?
Ans- Technical Skills for AWS Solution Architect jobs
Java/Python or C++
Networking
Data Storage Fundamentals
Security Foundations
AWS Service Selection
Cloud specific patterns & technologies
Personality skills for AWS Solution Architect jobs
Communication Skills
Time management skills
Flexibility & eagerness to learn
Business acumen
Ability to stay agile
Q9. What can I expect after this course?
Ans- After completing our AWS certifications training online, you will achieve:
Competent skills & knowledge, all ready to be utilized during the certification exam of AWS.
Smart & well-calculated ways to proceed & absorb in the lucrative AWS led job markets.
An AWS Training Certification online for training completion, by a highly recognized name - JanBask Training - declaring a successful completion of your learning-filled AWS training online for beginners to professionals. Our training completion certification gives you a great boost during interview calls.
Q10. What is the future scope of AWS career?
Ans- AWS has customers all across from over 190 countries - which covers millions of customers in 5000 education institutions, 127,500 nonprofit organizations, 2000 government agencies. AWS Data Services increased by a whopping 96% in just a single year - including Amazon ElastiCashe, Amazon RDS, Amazon Redshift, Amazon DynamoDB. AWS has over 70 services inclusive of storage, computing, database, networking, application services, analytics, management, deployment & mobile.
I hope that we were able to clear some air about AWS VPC for you. AWS or Amazon Web Services offers a wide array of services and also provides certifications to help you demonstrate your expertise in various cloud computing technologies. You can choose the best AWS certification courses according to your interest and job role. However, JanBask offers an AWS certification course to make things simpler for you. Read and then re-read everything for a better understanding. This is all we have in store for today. If you have any queries or comments, please leave them in the comments section below, and we shall get back to you soon.
 Pinterest
Pinterest
 Email
Email
The JanBask Training Team includes certified professionals and expert writers dedicated to helping learners navigate their career journeys in QA, Cybersecurity, Salesforce, and more. Each article is carefully researched and reviewed to ensure quality and relevance.

Cyber Security

QA

Salesforce

Business Analyst

MS SQL Server

Data Science

DevOps

Hadoop

Python

Artificial Intelligence

Machine Learning

Tableau
Search Posts
Related Posts
Cloud Computing and Cyber Security: Which One is Better?
![]() 6.3k
6.3k
Amazon Redshift vs Amazon RDS vs DynamoDB vs SimpleDB
![]() 15.6k
15.6k
AWS Object Storage and CDN (S3, Glacier and CloudFront)
![]() 4.7k
4.7k
11 Must Have Skills To Succeed As A Cloud Computing Engineer
![]() 4.5k
4.5k
AWS Certifications Guide: Know Everything About one of the Highest-Paying IT Certification
![]() 228.8k
228.8k
Receive Latest Materials and Offers on AWS Course
Interviews