10
JulInternational Womens Day : Flat 30% off on live classes + 2 free self-paced courses - SCHEDULE CALL
Sometimes Engineers have access to testing environments only, not the production environment. Here, we need log management tools that could take care of changes without disturbing the production environment. Here, we will introduce some of the most popular log management tools like Graylog Kibana Elk Logstash Splunk, etc. Out of all these, Graylog ELK Kibana are the most popular choices among developers. The objective of this blog Graylog vs ELK is to make you familiar with all these log management tools and how they are different. We will focus on Graylog vs Kibana, Elk vs Graylog, Graylog vs Splunk, etc. Before diving deep into the discussion for ELK vs Graylog, let us first discuss what log management is and why do need log management tools.
When working in an exemplary IT foundation you regularly confront the issue that engineers only have access to test or advancement conditions, yet not to production. To settle bugs or to have a look at the framework running underway, log document access is required. This is regularly impractical because of security necessities. The aftereffect of this circumstance is that the activity folks need to give these documents to the designers, which can take a specific measure of time.
An answer to these issues is to give a Log Management Server and concede access to the designers by means of a UI. Regardless of some business devices like Splunk, which is the true market pioneer around, there are some very encouraging open-source arrangements that do scale exceptionally well and may give enough highlights to take care of business.
Log management is the aggregate procedures and approaches used to direct and encourage the age, transmission, investigation, stockpiling, documenting and extreme transfer of the extensive volumes of log information made inside a data framework. A log, in a computing setting, is the consequently created and time-stepped documentation of occasions pertinent to a specific framework. For all intents and purposes, all product applications and frameworks create log records.
Compelling log management is basic to both security and consistency. Observing, reporting and breaking down framework occasions is an essential segment of security insight (SI). As to consistency, directions, for example, HIPPA, the Gramm-Leach-Bliley Act and the Sarbanes Oxley Act have explicit commands identifying with review logs.
Log management programming mechanizes huge numbers of the procedures included. An occasion log supervisor (ELM), for instance, tracks changes in an association's IT framework. These progressions are reflected in review trails that must be delivered for a consistency review.
DevOps Training & Certification Course

Let us discuss and try to differentiate pioneers of log management Graylog, ELK Stack, Kibana, Logstash, And Splunk. The blog covers the following topics.

In this blog for ELK vs Kibana, we will first discuss what Kibana is. Kibana is an open-source analytics and representation stage intended to work with Elasticsearch. You use Kibana to the pursuit, see, and associate with information stored in Elasticsearch records. You can without much of a stretch perform propelled information investigation and picture your information in an assortment of graphs, tables, and maps.
Read: What is Puppet? Puppet Tutorial Guide for Beginners
Graylog Kibana makes it easier to comprehend the huge volumes of information. It's straightforward, a program-based interface that empowers you to rapidly make and share dynamic dashboards and show changes to Elasticsearch questions progressively. Setting up Graylog Kibana is a snap. You can introduce Kibana and begin investigating your Elasticsearch files in minutes — no code, no extra infrastructure is required. Moving ahead, we will discuss about ELK log management tool

In this blog for Graylog vs Kibana, let us discuss what Graylog is and how it is considered as the best log management tool. We have already discussed Kibana in the previous section. In terms of log management, Graylog is a characterized platform that gathers, orders, and dissects both organized and unstructured information from any source.
These days most of the applications are following microservice design where many microservices are facilitated on various machines. In this way, it sets aside exceptionally immense time for the client to get the logs from every microservice on various machines inevitably.
To maintain a strategic distance from this we have an application called Graylog which works by designing at one place and getting the logs of all microservices at one centralized area.

In this section, our focus of discussion is ELK. We have already explained to you about Graylog and Kibana in the previous section. By consolidating the huge mainstream Elasticsearch, Logstash, and Kibana (what was the ELK Stack is presently the Elastic Stack), Elastic has made a start to finish stack that conveys noteworthy bits of knowledge progressively from an organized and unstructured information source.
Fabricated and upheld by the architects behind every one of these open source items, the Elastic Stack makes seeking and investigating information simpler than at any other time. A large number of associations overall utilize these items for a perpetual assortment of business basic capacities.

In this blog for Kibana vs Graylog, let us discuss what is Logstash in brief. Logstash is module-based information that gathers and handles motor. It accompanies a wide scope of modules that makes it conceivable effectively configuring it to gather, process and forward information in a wide range of models.
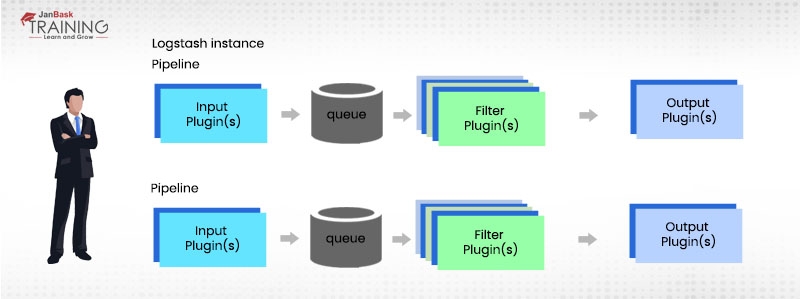
Handling is sorted out into at least one of the pipelines. In every pipeline, at least one information module gets or gathers the information that is then set on an inside line. This is as a matter, of course, little and held in memory, however, it can be designed to be bigger and endured on the circle to enhance unwavering quality and flexibility. Here is a screenshot of an image taken from the website of the stack share to explain the process to you.
Read: How to Learn DevOps and Become a DevOps Engineer | Complete Guide
Processing threads read information from the line in miniaturized scale clusters and process these through any arranged channel modules in succession. Logstash out-of-the-crate accompanies an expansive number of modules focusing on explicit sorts of preparing, and this is how information is parsed, handled and improved When the information has been prepared, the handling strings send the information to the fitting yield modules, which are in charge of arranging and sending information onwards, for example to Elasticsearch.
Input and output modules can likewise have a codec module designed. This permits parsing or potentially arranging of information before it is put onto the inside line or sent to a yield module.

In this blog for Graylog vs Splunk, let us discuss what is Splunk? you have a sound idea of graylog by reading our previous section. IT is the right to know about SPlunk and how it is different from Graylog and other log management tools.
Splunk is an amazing stage for investigating machine information. It’s the information that machines radiate in incredible volumes however which is only here and there utilized viably. The quickest method to comprehend the power and adaptability of Splunk is to think about two situations: one in the data center and one in the promoting office. Splunk produces programming for looking, checking, and investigating machine-created enormous information, by means of a web-style interface.>
Splunk assembled the majority of the important data into a focal list that you could quickly seek. Splunk can give a nitty-gritty window into what's going on in your machine information. Splunk can likewise uncover chronicled patterns, relate numerous wellsprings of data, and help in a great many different ways.
DevOps Training & Certification Course

This section “ELK vs Graylog vs Kibana vs Logstash vs Splunk” explains the healthy differences among popular log management tools. Splunk and the ELK Stack utilize two distinct ways to deal with taking care of a similar issue. Splunk takes a heap of information and enables individuals to seek through the data to extricate what they require. ELK requires more work and arrangement to start with, however, the esteem extraction is less demanding towards the end.
Read: Know Everything About DevOps Engineer & Architect Salary
Elastic has assembled seemingly the most prominent log the board stage for both open source and business (cloud and endeavor) log observing devices. The Elastic Stack—all the more regularly known as ELK Stack—consolidates Elasticsearch, Logstash, and Kibana. Elasticsearch is a cutting-edge look and investigation motor dependent on Apache Lucene, while Logstash gives information preparing and improvement. Kibana offers logs of revelation and visualization.
ELK is a combo of three separate administrations. Every one of them is open-source and created by a similar group.
Moving ahead, let us discuss Graylog vs Splunk and which tool you should opt for. Splunk is a platform for analyzing, investigating and envisioning the machine-produced information assembled from the sites, applications, sensors, gadgets and so forth covering the whole framework scene. It speaks with various log records and stores documents information as occasions into nearby files. It gives the simplest method for hunting capacities and has a wide cluster of alternatives to gather logs from numerous sources. Splunk is accessible in both SaaS and undertaking releases.
Graylog is an elective log that tends to the downsides of the ELK stack and is very developed. It gives a UI and a server part. In addition, Graylog utilizes Elasticsearch as a database for the log messages and additionally MongoDB for application information.
The UI does essentially what a UI does. It makes the information open in an internet browser.
The server part gives a predictable administration of the log records. The Graylog server has the accompanying highlights:
Also, Graylog can without much of a stretch be sent in a bunched situation, so you get high accessibility and load distribution. To make a full arrangement, it is appropriate to join Graylog with Logstash with a touch of fixing of Logstash and a custom Graylog Plugin.
The blog for ELK vs Graylog vs Kibana vs Logstash vs Splunk gives you a sound idea of log management fundamentals and related tools. Log management can come in very handy at a lot of places. All you have to do is to figure out which technology you should use for your concern. Other than the features and usability you also need to see if it is affordable by your concern. All these tools and software come with a different price tag. Before you make the final decision, don’t forget to consider significant differences among all log management DevOps tools, Graylog vs Kibana, Elk vs Graylog, Graylog vs Splunk, and make a sound decision. We wish you luck!
 Pinterest
Pinterest
 Email
Email
A dynamic, highly professional, and a global online training course provider committed to propelling the next generation of technology learners with a whole new way of training experience.

Cyber Security

QA

Salesforce

Business Analyst

MS SQL Server

Data Science

DevOps

Hadoop

Python

Artificial Intelligence

Machine Learning

Tableau
Search Posts
Related Posts
Receive Latest Materials and Offers on DevOps Course
Interviews