24
JulGrab Deal : Flat 30% off on live classes + 2 free self-paced courses - SCHEDULE CALL
Grab Deal : Flat 30% off on live classes + 2 free self-paced courses - SCHEDULE CALL
AWS shared responsibility model lies at the foundation of AWS security and helps enterprises to improve the overall security of the cloud environment. The implementation of the AWS shared responsibility model is not the sole responsibility of one player but it is shared between AWS and the customer.
You have to understand which security controls are AWS’s responsibility and which are yours. With a solid understanding of the AWS shared responsibility model, it is easy to build and maintain a high-security environment. Enhance your career with our AWS Certification course that helps you qualify the AWS Solution Architect Certifications and ensures that you are ready to excel in your current/future job role.
Before enrolling for AWS Courses, gain an in-depth knowledge about cloud computing through our Cloud Computing Certification Courses.
In every aspect, security is considered the major priority by AWS. During the last few years, enterprises were reluctant to adopt a cloud environment due to security reasons. To overcome this hesitation, AWS needs to be at the top of security excellence and governance. AWS has become a popular security standard today serving most security - sensitive customers around.
AWS services are distributed or deployed exactly the same way throughout their entire global infrastructure. Also, document backup is covered by the same strict security standards for large corporations. AWS is responsible for the global security of the cloud as a whole while customers are responsible to maintain the security of their specific instances. If you are confused about which AWS Certification to choose, here’s an easy solution. Read our blog on the best AWS Certifications in 2022 and choose the right one for yourself.
AWS Solution Architect Training and Certification

When a customer chooses any of the Amazon’s infrastructure as a service, he needs to perform all the necessary configurations and management tasks as follows:
An AWS Cloud practitioner has a wide range of roles and responsibilities to perform. Learn about the roles and responsibilities of an AWS Solutions Architect from this blog.
|
AWS Responsibilities |
Customer Responsibilities |
AWS Shared Responsibilities |
|
|
|
AWS provides the requirements for the infrastructure and the customer must provide their own control implementation within their use of AWS services:
Get to know more about AWS from our blogs and resources at JanBask Training.
To help you in better understanding, the AWS shared responsibility model, it has been divided into three major categories:
AWS infrastructure security elements include regions, edge locations, availability zones and the foundations of their compute, database and network services. AWS controls access to their data centers where sensitive customer data is stored.
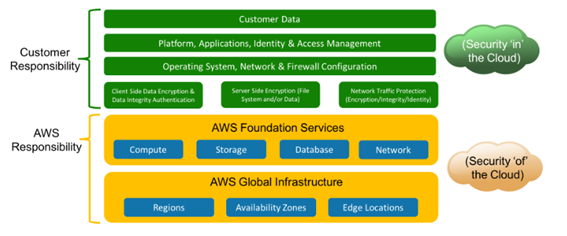
It covers physical access to networking and hardware components, additional data center facilities like UPS systems, generators, PDUs, fire suppression systems etc. Majorly, AWS is responsible for components management that makes up the cloud and stored within your system.
When global infrastructure is secured and maintained by the AWS, the responsibility for firewall configurations, OS configuration, network management, IAM, and application security falls on the customers. If the customer wants to add extra security features then it is entirely based on him. An AWS Solution Architect has to shoulder multiple responsibilities and so you need to know the complete AWS Solutions Architect Certification path details before you sit for your exam.
It is usually decided on the basis of the nature of a business and existing security controls. It is recommended tightening security to the maximum extent with minimum exposure to external threats that could compromise your environment. The important thing to focus here is that AWS offers many powerful security controls but how to apply them in your favor is your responsibility, not the AWS.
Are you preparing for your AWS Solutions architect interview? Learn about the top AWS Solutions Architect interview questions and answers from our blog.
The popular Container services in AWS include:
AWS Elastic Map Reduce (EMR)
AWS Relational Database Service (RDS)
AWS Elastic Beanstalk
It is clear that application management with OS and network configuration has shifted to being the responsibility of AWS and no longer down to us as the customer to manage. This is the major difference between infrastructure-based services and container-based services in AWS.
However, not all responsibilities are shifted. You can notice clearly that firewall configuration remains with the end-user which integrates at the application management level.
Get started to test your AWS subject knowledge with this fun and interesting Quiz on AWS.
AWS Solution Architect Training and Certification

The popular abstract services in AWS include:
Here, you can notice that more responsibilities are shifted to AWS mainly network traffic protection and encryption. The customer is responsible for IAM, client-side data encryption and data integrity encryption majorly at the abstract layer. As we progress through the layers in the Aws share responsibility model, it is clear that control and responsibilities shift more towards AWS and customer becomes free. Get to know about the Top 10 AWS Certifications for I.T professionals in 2022.
You can clearly observe the difference below between different layers of the model how responsibilities are shared and shifted to the AWS one by one. To choose the right AWS model for your business, you should analyze the business requirements first and try to know which method can deliver the best results based on your needs. It is not an easy task for the customer reaching the final decision. So, it is recommended taking helps from AWS experts and learn about the best AWS shared responsibility model for your business.
The AWS shared responsibility model is designed to maximize the overall security of Amazon’s cloud infrastructure. By educating their customers on how to manage or maintain strong operational protections, both Amazon and customers can feel more protected.
The mutual responsibilities of shared security gives assurance to Amazon that they don’t have to manage every security aspect directly and helps customers feel like Amazon can adjust to their specific security needs.
When security responsibilities are shared, customer awareness is the key with a deep understanding of risks associated with trusting a third-party. This freedom can be a huge set for lowering down the costs and increasing the overall quality of services.
To know more on Shared responsibility model and its implementation, learn practical aspects of the cloud with JanBask Training and join our AWS certification course to become a valuable IT resource in the cloud domain.
AWS Solution Architect Training and Certification

Q1. Why is AWS so popular?
Ans- AWS or Amazon Web Services is a subsidiary of Amazon that specializes in cloud computing platforms that offer scalable and cost-effective cloud computing services. It provides distributed computing processing capacity and software tools to individuals and companies.This architect is the most flexible and more secure than a company hosting its own website.
Q2. What are some of the components of AWS?
Ans- AWS provides an array of components. They are-
i) Data Management
ii) Data Transfer
iii) Storage
iv) Networking
v) Compute
vi) Visualization
Q3. What are some of the AWS Cloud services?
Ans- Some of the AWS Cloud services are as follows-
Q4. Why AWS certifications are important?
Ans- AWS certifications are important to have as they:
Q5. What is included in the course of AWS Certification?
Ans- Here are all that you will learn:
Q6. Which AWS Certifications are in demand?
Ans- Here are the few in-demand AWS certifications that you may consider qualifying after finishing our intensive & real-industry assignments based training for AWS:
Q7. What are the required skills for AWS?
Ans- Technical Skills for AWS Solution Architect jobs
Personality skills for AWS Solution Architect jobs
Q8. What can I expect after this course?
Ans- After completing our AWS certifications training online, you will achieve:
Q9. Do you help with resume building and interview preparation?
Ans- Yes, we help with drafting and reviewing your resume for the AWS jobs too. Our trainers are from the direct working industry and they know what kind of resume/CV the recruiters hiring for AWS roles expect from the professionals. They know how resumes are needed to be built from scratch. You just share your briefs, info and they will explain to you how to frame your entire resume without any gaps or committing any mistakes. A carefully drafted resume is a source via which recruiters narrow down the name of the interviewee. So drafting a careful & professional resume is very important to become a top preference during the interview.
Q10. What is the future scope of AWS professionals?
Ans- AWS has customers all across from over 190 countries - which covers millions of customers in 5000 education institutions, 127,500 nonprofit organizations, 2000 government agencies. AWS Data Services increased by a whopping 96% in just a single year - including Amazon ElastiCashe, Amazon RDS, Amazon Redshift, Amazon DynamoDB. AWS has over 70 services inclusive of storage, computing, database, networking, application services, analytics, management, deployment & mobile. AWS has over 1 million customers associated with it, which means job opportunities in this field are extravagant.
The JanBask Training Team includes certified professionals and expert writers dedicated to helping learners navigate their career journeys in QA, Cybersecurity, Salesforce, and more. Each article is carefully researched and reviewed to ensure quality and relevance.

Cyber Security

QA

Salesforce

Business Analyst

MS SQL Server

Data Science

DevOps

Hadoop

Python

Artificial Intelligence

Machine Learning

Tableau
Interviews